One of the recent additions to Oracle Cloud Infrastructure (OCI) is IAM Domains. New OCI tenancies are provisioned with IAM Domains and at time of writing tenancies with IDCS instances are being migrated to IAM Domains.
I originally created Peek to create a visual representation of effective user permissions inside an OCI tenancy to assist with performing user access reviews. Excessive permissions and IAM misconfigurations are a common issue found in cloud environments that can lead to privilege escalation and/or unauthorised access to resources and data.
At time of writing the latest release of the OCI CLI now supports interacting with IAM Domain resources and so I have created a version of Peek that works with IAM domains.
I’ve also streamlined the setup, meaning you only need to run a single Docker container and no longer need to set up an APEX instance to visualise the data.
Setup & Running Peek for IAM Domains
Before running Peek you will need:
- A Docker environment to run the Peek container,
- An OCI-CLI config file, and valid OCI API key for a user with read permissions in your tenancy.
Running the docker container is straight forward:
docker run -it --name peek \
--mount type=bind,source=/full/path/to/.oci,target=/root/.oci/,readonly \
-e OCI_TENANCY_OCID=<your tenancy OCID> \
-e OCI_PROFILE_NAME=<your OCI config profile name> \
-e TOOLTIP_LINE_PX=20 \
-p 4567:4567 \
--rm scottfletcher/peek-domainIn the above command you’ll need to replace:
- “/full/path/to/oci” with the full path to your OCI config directory, as an example mine is /home/scott/.oci
- <your tenancy OCID> with the tenancy OCID of the tenancy you wish to run this for.
- <your OCI config profile name> with the name of the profile in the OCI config that matches the tenancy OCID. As an example mine is DEFAULT.
Optionally you can also configure the port mappings. The web server inside the container is listening on port 4567 so in the example above I’m mapping that to the host, but you can change the host port if required.
Also, Peek will by default set the height of each line to 20px. Depending on how long your policy statements are you might need to set a larger tooltip value to see all the statements in the tooltip. To change the line height and subsequent tooltip height specify a larger value for the TOOLTIP_LINE_PX environment variable.
After running the command you should see:
Unable to find image 'scottfletcher/peek-domain:latest' locally
latest: Pulling from scottfletcher/peek-domain
Digest: sha256:d16076f99088942bd9d630ef8372869d764bd9fad07c57156c45762d06c98d1a
Status: Downloaded newer image for scottfletcher/peek-domain:latest
2023-03-20T00:15:36.963787Z mysqld_safe Logging to '/var/log/mysql/error.log'.
<snip>
2023-03-20 00:15:57,376 INFO RPC interface 'supervisor' initialized
2023-03-20 00:15:57,376 CRIT Server 'unix_http_server' running without any HTTP authentication checking
2023-03-20 00:15:57,376 INFO supervisord started with pid 209
2023-03-20 00:15:58,380 INFO spawned: 'mysqld' with pid 211
2023-03-20 00:15:58,384 INFO spawned: 'ruby' with pid 212
2023-03-20 00:15:59,446 INFO success: mysqld entered RUNNING state, process has stayed up for > than 1 seconds (startsecs)
2023-03-20 00:15:59,446 INFO success: ruby entered RUNNING state, process has stayed up for > than 1 seconds (startsecs)At which point you can browse to http://localhost:4567 and you will see a live progress bar:
Depending on the size of your tenancy, the number of domains, compartments, groups, users, and policy statements this process can take some time. Please be patient.
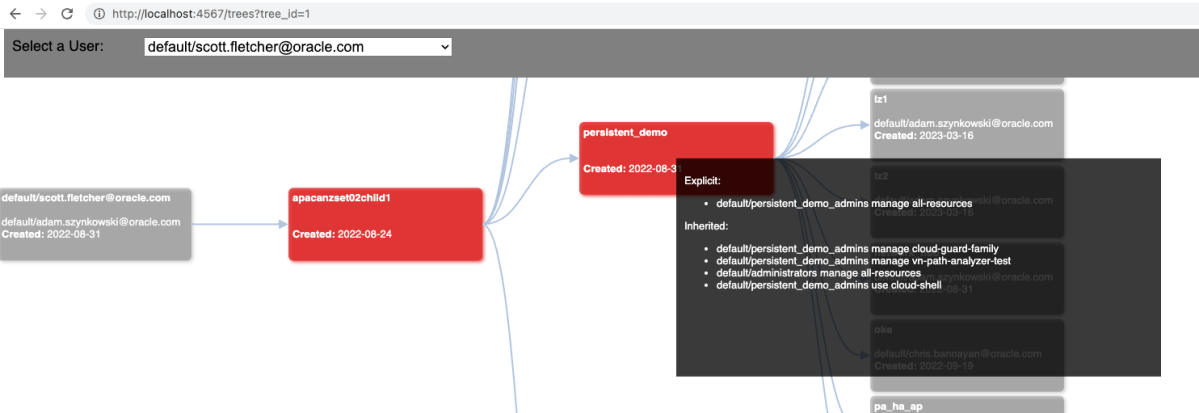
When complete the first user’s permission tree will be shown:

The boxes represent the compartments present in the tenancy. Also shown is the user who created them and on which date. If the created by username isn’t shown then you will need to enable default OCI tagging.
To view another user’s permissions select the user from the drop down menu.
As with the Peek IDCS version, the colours represent the maximum permission explicitly defined for that compartment:
- Red: A policy statement with manage permissions has been defined,
- Orange: A policy statement with use permissions has been defined,
- Yellow: A policy statement with read permissions has been defined,
- Green: A policy statement with inspect permissions has been defined.
If you have a large diagram you can collapse the structure by clicking on a compartment. You can also scroll, and click and drag the diagram around to see any tooltips on the right hand side that may be hidden off screen.
If you have any questions, or feedback feel free to leave a note in the comments.

One thought on “OCI IAM Domains User Access Review”