So far, I have discussed generic concepts, IAM, Networking and Key Management pertaining to OCI Gen-2 Cloud. In this part I am going to discuss the Edge Security Service that is available in Oracle Cloud Infrastructure OCI Gen-2 Cloud. OCI Edge Dyn Security services protect Applications and APIs in the multi-cloud environments.
Continue reading “Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part V (Edge Security Services)”Author: Raminder Bhrara
Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part IV (Key Management)
So far, I have discussed generic security concepts, IAM and Networking pertains to OCI Gen-2 Cloud. In this part I am going to discuss the Key Management Service that is available in Oracle Cloud Infrastructure OCI Gen-2 Cloud.
Oracle Cloud Infrastructure Key Management Service OCI KMS is a managed service that provides you with centralized management of the encryption of your data. KMS can be used to create master encryption keys and data encryption keys. KMS helps to rotate keys to generate new cryptographic material, enable or disable keys for use in cryptographic operations, assign keys to resources, and use keys for encryption and decryption.
Continue reading “Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part IV (Key Management)”Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part III (Networking)
In my previous blog posts, I have discussed the generic security concepts and Identity and Access Management in OCI. This part of the series discusses OCI Networking Service. Its concepts and best practices for securing networks in OCI.
High-throughput and reliable networking is fundamental to public-cloud infrastructure that delivers compute and storage services at scale. As a result, Oracle has invested significant innovation in Oracle Cloud Infrastructure networking to support requirements of enterprise customers and their workloads. Oracle Cloud Infrastructure regions have been built with a state-of-the-art, non-blocking Clos network that is not over-subscribed and provides customers with a predictable, high-bandwidth, low latency network. The data centers in a region are networked to be highly available and have low-latency connectivity between them.
In this post, I will go into depth on the components that make up the networking layer, and the security rules which can be applied to them.
Continue reading “Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part III (Networking)”
Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part II (Identity and Access Management)
In my previous blog post Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part I , I have discussed the seven pillars of information security upon which Oracle Cloud Infrastructure OCI (Oracle Gen-2 Cloud) is built. The cloud shared security and responsibility model was discussed along with the concepts such as Regions, Availability Domains and Fault Domains. This part discusses the Identity and Access Management for OCI. It provides authentication and authorisation for all the OCI resources and services.
An enterprise can use single tenancy shared by various business units, teams, and individuals while maintaining the necessary security, isolation, and governance, and this post will go into the concepts involved in this.
Continue reading “Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part II (Identity and Access Management)”Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part I
Previously, I have discussed Oracle’s overall information security portfolio in blog entry – Oracle Information Security – Where it begins, Where it ends. It was pertaining to information security in Oracle Cloud Infrastructure – Classic and On-Premises suite of products including Identity and Access Management and Database Security.
In a series of five blog posts, I am going to cover the security concepts in Oracle Cloud Infrastructure (aka OCI or Oracle Gen-2 Cloud). The Oracle Cloud Infrastructure (OCI) is a trusted enterprise cloud platform that offers customers deep control with unmatched security. It provides Oracle customers with effective and manageable security to confidently run their mission-critical workloads and store their data.
Continue reading “Oracle Cloud Infrastructure OCI Gen-2 Cloud Security – Part I”Active Directory Delegated Authentication in Oracle Identity Cloud Service
AD Delegated Authentication is a way to synchronise user passwords between an on-premises Microsoft Active Directory enterprise directory structure and Oracle Identity Cloud Service (IDCS). Users can use their AD passwords to sign in to IDCS to access resources and applications protected by Oracle IDCS. We will use Office365 as one of the target applications. Oracle IDCS can provision user into Office365 and keep users synchronised.
The following diagram 1 depicts the scenario:

Diagram 1: Logical architecture of scenario
Continue reading “Active Directory Delegated Authentication in Oracle Identity Cloud Service”
Oracle Cloud Security is Openly Social
Oracle Identity Cloud Service (IDCS) protects Oracle IaaS, PaaS, SaaS and On-Premises applications. Oracle IDCS provides federated single-sign on experience to its clients. It follows open standards such as SAML 2.0, OAuth 2.0 and OpenID Connect 1.0. In the federation model, Oracle IDCS can either act as an Identity Provider (IdP) or a Service Provider (SP) or both.
Oracle IDCS has a built-in feature that provides multiple social identity providers such as Google, Facebook, LinkedIn and Twitter. It uses underlying OAuth 2.0 protocol to interact with the Social Identity providers. This article presents how to configure IDCS to allow for Social Logins. Let me explain this concept with the sequence diagram below:
ORACLE INFORMATION SECURITY – Where It Begins, Where It Ends
Background and Introduction
Targeted cyber intrusions remain the biggest threat to government ICT systems. Since opening in early 2010, the Australian Cyber Security Centre (ACSC) has detected and responded to thousands of these intrusions. These attacks are dealing with the Zero-Day exploits, DoS, DDoS, SQL Injections, Phishing, Ransomware, Large XML payloads and many other innovative attacks on IT systems.
You should never assume that your information is of little or no value. Adversaries are not just looking for classified information. A lot of activity observed by the ACSC has an economic focus, looking for information about Australia’s business dealings, its intellectual property, its scientific data and the government’s intentions.
The advent of cloud has challenged the traditional Security Operations Centres because users are outside the traditional network boundaries and they are using channels such as Mobile and Social. Modern IT Security attacks therefore become unpredictable. They are not carried out by humans but mobile devices or IoT Botnets. These attacks are adaptive in nature that remain dormant for some time waiting for an event to happen. These Advanced Persistent Threats (APT) in the Kill Chain process are inevitable and unpredictable.
Challenges faced by Cyber Security Operations Centre
Modern security attacks are not hard to plan against because many enterprises today have a traditional Security Operations Centre (SOC). There are many challenges that traditional Cyber Security Operations Centres (CSOCs) are facing in today’s world. There are too many monitoring tools and data but no real insight. A traditional SOC is built upon traditional security infrastructure deployed within the corporate network, and was originally designed to protect applications and users on the network. Following are the issues that are faced by traditional Security Operations Centre:
Too many silos
A traditional SOC purviews the corporate network, not your applications and data residing in the cloud. Analysts say that on an average, most enterprises today have applications on about 6 different cloud service providers. In the Identity Management space, I’m sure all of you are adapting to meet the needs of both on premises applications as well as modern cloud apps. What use is a SOC that looks inward to your own network, and provides no protection for your data residing on that many cloud service providers?
Too much data
Previous generations of management tools expect that human intelligence will draw conclusions out of the data, but human operators are already overwhelmed with the velocity and volume of alerts and data coming their way, and so they get tired and miss things. Your SOC analysts struggle with too many alerts, generated from a disparate bunch of security products deployed alongside each other. The classic Target breach that happened a couple of years ago could have been detected promptly, if only the alerts could have been acted upon in a timely manner, instead of being lost in a sea of other less-important alerts.
Too little actionable insight
Other tools have attempted to apply more advanced analytical techniques, but have only done so to subsets of the data because it’s too compute-intensive to do it across the board, so human operators are still required to stitch together information out the data silos.
Shortage of good Cyber Security resources
Your SOC operations complains of a constant shortage of resources. Skilled cybersecurity professionals are a sought-after resource, and with good reason. That is because most of the processes in a traditional SOC are manual, requiring human intervention to triage and act upon issues. Very little is automated.
I’m sure many of you can relate to the problem of shortage of resources as well, since staffing modern Identity Management operations, especially across on-premises legacy applications and modern cloud applications, is a challenge too in today’s market.
Users are the new perimeter
Traditional SOCs are based on a static “prevent-and-defend” philosophy, designed to keep the bad guys out of the network. They do not adapt contextually to the prospect of an attacker getting onto your network.
In the Identity Management space, I’m sure most of you can relate to the need for contextual application access control policies. Many Identity Management vendors provide such capabilities today – of detecting and alerting when user activity appears suspicious. For example, when a user who typically logs in during US business hours from a fixed location in the US, is suddenly detected to login from a new browser, a new location, and in the late hours of the night US time.
TOP 4 ASD Recommended Mitigation ICT Strategies
The threat is real, but there are things every organisation can do to significantly reduce the risk of a cyber intrusion. In 2009, based on our analysis of these intrusions, the Australian Signals Directorate (ASD) produced Strategies to Mitigate Targeted Cyber Intrusions – a document that lists a variety of ways to protect an organisation’s ICT systems. At least 85% of the intrusions that ASD respond involve adversaries using unsophisticated techniques that would have been mitigated by implementing the Top 4 mitigation strategies as a package. According to ASD Information Security Manual and Information Security Advice, the Top 4 mitigation strategies are:
Application Whitelisting
This when implemented correctly ‘Application Whitelisting’ makes it harder for an adversary to compromise an organisation’s ICT system. This allows only specifically authorised applications to run on a system. This is better than Blacklisting an application. This is because only known vulnerabilities can be blocked. Since hackers are getting innovative they will find a new way to overcome this hurdle. This is the reason Application Whitelisting is preferred.
Patching Systems
A software patch is a small piece of software designed to fix problems or update a computer program. Patching an organisation’s system encompasses both the second and third mitigation strategies. It is important to patch both your operating system and applications within a two-day timeframe for serious vulnerabilities. Once a vulnerability in an operating system or application is made public you can expect malware to be developed by adversaries within 48 hours. In some cases, malware has been developed to take advantage of a publicly-disclosed vulnerability within eight hours.
There is often a perception that by patching a system without rigorous testing, something is likely to break on the system. In most of cases, patching will not affect the function of an organisation’s ICT system. Balancing the risk between taking weeks to test patches and patching serious vulnerabilities within a two-day timeframe can be the difference between a compromised and a protected system.
Restricting Administrative Privileges
When an adversary targets a system, they will primarily look for user accounts with administrative privileges. Administrators are targeted because they have a high level of access to the organisation’s ICT system. If an adversary gains access to a user account with administrative privileges they can access any data the administrator can access – which generally means everything. Minimising administrative privileges makes it more difficult for the adversary to spread or hide their existence on a system.
Administrative privileges should be tightly controlled. It is important that only staff and contractors that need administrative privileges have them. In these cases, separate accounts with administrative privileges should be created which do not have access to the internet. This reduces the likelihood of malware infecting the administrator as they should not be web browsing or checking emails while using their privileged account. It is also important that once the staff is finished with their administrator privileges they are removed from those privileges.
Creating a Defence-In-Depth System
As a package, these mitigation strategies are highly effective in helping achieve a defence-in-depth ICT system. The combination of all four strategies, correctly implemented, will help protect an organisation from low to moderately sophisticated intrusion attempts. Put simply, they will make it significantly more difficult for an adversary to get malicious code to run on your ICT system, or continue to run undetected. This is because the Top 4 strategies enable multiple lines of defence against cyber intrusions.
Of course, implementing the other strategies will provide additional protection for ICT system. Several strategies have an overall security rating of ‘excellent’ which means that they are the most effective measures to protect ICT systems. However, an organisation should also conduct a risk assessment and implement other mitigation strategies as required to protect its ICT system.
Concept of Identity Security Operations Centre (Predict – Prevent – Detect – Respond)
IT threats are multi-vector. The ability to correlate anomalous events from the network, applications and user behaviours is key in early detection and containment. Identity is now the bridge between user, application and network controls. It is the identity context brought together with technologies such as machine learning, big data and advanced analytics that allows a security professional to centralise and normalise user activities. Therefore, Identity SOC must protect users, applications, APIs, content and data as well as workloads.
The Identity SOC utilises optimised dashboards and risk console for security professionals that is bringing in feeds from throughout the environment such as following:
- Security Tools including firewalls, Intrusion Detection System, Intrusion Prevention System, Web Proxies, Virtual Private Networks, Data Loss Prevention Systems, Web Application Firewalls and Vulnerability Assessment scanners
- Applications and Workloads whether on-premises or in the cloud
- Infrastructure such as IaaS, PaaS, middleware, database, web servers, enterprise mobility management, hypervisors and hosts
- Networking tools such as routers, switches, DNS, DHCP and load balancers
Identity SOC includes automated orchestration and incident response management. Bi-directional integrations allow it to be self-healing enabling different departments to work together through organised playbooks and processes.
Introducing Oracle Information Security Portfolio
Oracle is making a big investment in the world’s first Identity SOC. With new security cloud services that integrate several new technologies into a homogeneous set of services. The integrated technologies include Security Incident and Event Management (SIEM), User & Entity Behaviour Analytics (UEBA), Identity Management (IDM), API Platform Cloud Service (APICS) and Cloud Access Security Broker (CASB). Each of these new services will integrate with the rest of security fabric, but when joined together they offer the full benefit of an identity SOC with bi-directional controls and actionable intelligence.
Oracle offers a comprehensive information security portfolio. It provides Information Security for browser based web applications, mobile application and business-to-business applications and systems. Oracle Information Security provides defence in depth by having rich Database Security functions and services. The following diagram depicts the functional aspect of Oracle Information Security:

Oracle Information Security is a complete end-to-end IT Security portfolio from Cloud to On-Premises to Hybrid Cloud Information Security. The following diagram depicts the operational aspect of Oracle Information Security:
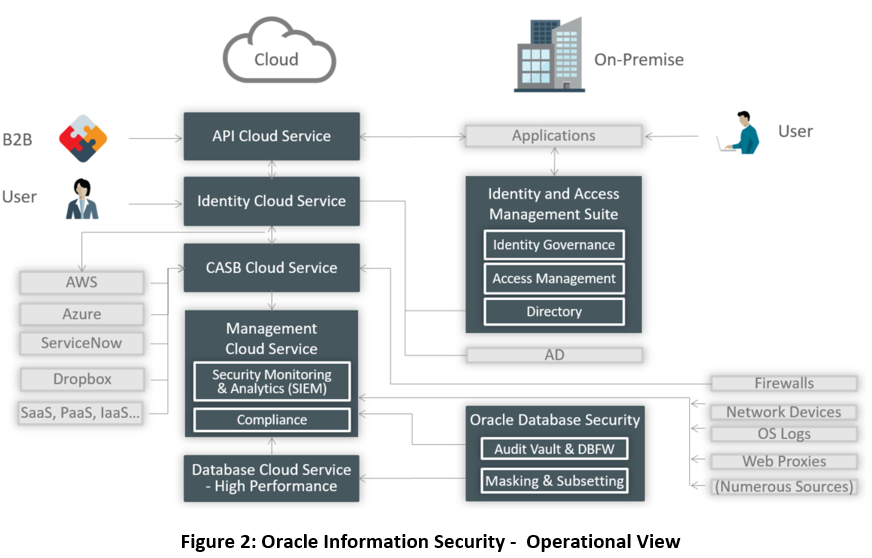
The following sections briefly describe the Oracle Information Security portfolio from the functional viewpoint. Oracle information security portfolio can be divided into Oracle Cloud Security, Oracle Hybrid Security and Oracle On-Premises Security.
Oracle Cloud Security – Oracle Cloud Infrastructure (Classic)
Oracle Cloud Security offers the most complete identity and security solution for providing secure access and monitoring of hybrid cloud environment and addressing all IT governance and compliance requirements. Oracle Cloud Security delivers an identity Security Operations Centre (SOC) providing actionable intelligence and bi-directional control through a combined offering of Security Information and Event Management (SIEM), User Entity Behaviour Analytics (UEBA), Cloud Access Security Broker (CASB) and Oracle Identity Cloud Service (IDCS).
Oracle Cloud Security follows a shared responsibility model. The figure below depicts the same:
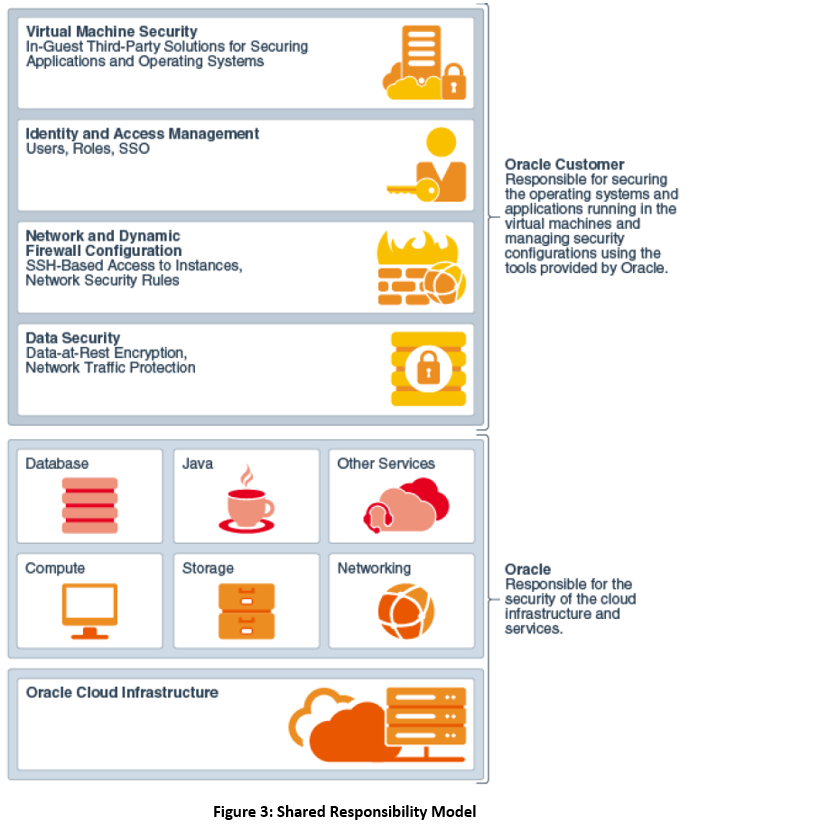
The following presents the brief overview of each of the Oracle Cloud Security Service:
Oracle Identity Cloud Service
Modern cloud applications require modern identity and access management (IAM) architectures. There is a need for IAM solutions offered as identity cloud services (IDaaS). As enterprises use more software applications as services (SaaS), platform as a service (PaaS) and infrastructure as a service (IaaS), they must provision users and oversee the rights that are assigned to them, quickly and easily.
Oracle Identity Cloud Service (IDCS) is Oracle’s next-generation IDaaS platform built on modern cloud principles using open identity standards to address these challenges. This platform delivers innovative and fully integrated IAM capabilities through a multi-tenant cloud that can be leveraged by other cloud-based services.
Oracle Cloud Access Security Broker
Oracle Cloud Access Security Broker (CASB) is the service that gives visibility and insight into both enterprise’ entire cloud stack and deep information about the cloud services that are getting utilised by the enterprise within security controls.
Oracle CASB is the service that is used for the following:
- Threat Detection: Identify existing threats to your cloud footprint by leveraging real-time threat intelligence feeds and machine learning techniques to establish security baselines and to learn behaviour patterns
- Predictive Analysis: Stay a step ahead of threats with patent-pending modelling techniques that evaluate risks across hundreds of threat vectors to provide you with a concise summary of potential threats
- Automated Incident Response: Keep enterprises secure by automating responses to threats with forensics, incident management, orchestration and remediation through native capabilities as well as integration with existing technologies
- Security Configuration Management: Eliminate labour intensive, error prone manual processes and manages security configurations within cloud applications by asserting configurations as well as continuously enforcing them
Oracle Management Cloud
Oracle Management Cloud (OMC) is a suite of next-generation integrated monitoring, management, and analytics cloud services that leverage machine learning and big data techniques against the full breadth of the operational data set. OMC’s Unified Platform helps customers improve IT stability, prevent application outages, increase DevOps agility and harden security across their entire application and infrastructure portfolio.
Following sections discuss the aspects of OMC that are related to IT Security:
Oracle Log Analytics
Oracle Log Analytics Cloud Service monitors, aggregates, indexes, and analyses all log data from your applications and infrastructure – enabling users to search, explore, and correlate this data to troubleshoot problems faster, derive operational insight, and make better decisions.
Security Monitoring and Analytics Cloud Service
Oracle Security Monitoring and Analytics (SMA) Cloud Service enables rapid detection, investigation and remediation of the broadest range of security threats across on-premises and cloud IT assets. Security Monitoring and Analytics provides integrated SIEM and UEBA capabilities built on machine learning, user session awareness, and up-to-date threat intelligence context.
Configuration and Compliance Cloud Service
Oracle Configuration and Compliance Service enables the IT and Business Compliance function to assess, score and remediate violations using industry standard benchmarks in addition to your own custom rules. The Oracle Configuration and Compliance Service can assess both on premise and cloud infrastructure.
Oracle API Platform Cloud Service
Oracle API Management solution supports agile and secure API development and makes it easy to keep an eye on KPIs covering every aspect of the API lifecycle. True hybrid API deployment – in the Cloud or on-premises – means that API solution is modern and adaptable, all while employing the most up-to-date security protocols. It provides the virtualisation layer and protects APIs against DDoS, SQL injection and XML attacks etc.
Oracle Hybrid Cloud Security
Oracle Information Security provides state-of-the-art Hybrid Cloud security. It is a well-known fact that Organisations are not going to migrate to the cloud overnight. Therefore, organisations need an information security solution for a hybrid cloud. Oracle Information Security offers the following for the hybrid cloud:
AD Integration
Oracle Identity Cloud Service provides tools for a seamless integration with Microsoft Active Directory (AD) platform:
- Bridge: The bridge continuously reconciles AD users and groups to Oracle Identity Cloud Service. No need to propagate entries manually.
- Federated SSO with ADFS: The SAML integration provides SSO between Active Directory Federation Services (ADFS) users and Oracle Identity Cloud Service.
With AD platform fully integrated to Oracle Identity Cloud Service, AD users in the cloud are kept in sync without any management effort.
OIM Integration
Oracle Hybrid Security provides OIM Cloud Connector through which the users get provisioned into Oracle Identity Cloud service in an automated fashion
IdP Federation
Oracle Identity Cloud Service can federate with other Identity Providers IdP. This is done through open standards such as SAML, OpenID Connect and OAuth open standard protocols. Oracle IDCS can be federated with Social Identities such as Google, Facebook, Twitter and LinkedIn.
OAM Integration
Oracle Identity Cloud Service and Oracle Access Manager on-premises component can be integrated as Service Provider and Identity Provider and vice versa. They both talk SAML 2 protocols through which a trust can be established between the two.
On-Premises Information Security
Oracle Identity Management provides a unified, integrated security platform designed to manage user lifecycle and provide secure access across the enterprise resources, both within and beyond the firewall and into the cloud. The Oracle Identity Management platform provides scalability with an industry-leading suite of solutions for identity governance, access management and directory services.
Oracle Identity Governance
Oracle Identity Governance is a solution that provides self-service, compliance, reconciliation, provisioning and password management services for applications residing on-premise or on the Cloud. Oracle Identity Governance and Administration is placed in the leaders quadrant in Gartner Magic Quadrant that can be reached on the following URI:
https://www.gartner.com/doc/reprints?id=1-4POUQXH&ct=180126&st=sb
Oracle Access Management
Oracle Access Management provides an enterprise-level security platform, delivers risk-aware end-to-end user authentication, single sign-on, and authorization protection. The Oracle Access Management enables enterprises to secure access and seamlessly integrate social identities with application. Oracle Access Management is placed in the leaders quadrant in Gartner Magic Quadrant that can be reached on the following URI:
https://www.gartner.com/doc/reprints?id=1-42A5TO6&ct=170607&st=sb
Oracle Directory Services
Oracle Directory Services provides a comprehensive directory solution with storage, proxy, synchronization and virtualization capabilities. With this unifying approach, it provides the services required for both enterprise and carrier-grade environments, including scalability to billions of entries, easy installation, elastic deployments, enterprise manageability, and effective monitoring.
Oracle Database Security – Defence-in-Depth
Oracle Database provides a rich set of security features to manage user accounts, authentication, privileges, application security, encryption, network traffic, and auditing.
Oracle Advanced Security
Oracle Advanced Security comprises of two features: Transparent Data Encryption and Oracle Data Redaction. The following defines these features:
- Transparent Data Encryption: Transparent Data Encryption (TDE) enables you to encrypt data so that only an authorized recipient can read it
- Data Redaction: Oracle Data Redaction enables you to redact (mask) column data using several redaction types. Following presents different redaction types:
- Full redaction. You redact all the contents of the column data. The redacted value that is returned to the querying user depends on the data type of the column. For example, columns of the NUMBER data type are redacted with a zero (0) and character data types are redacted with a blank space.
- Partial redaction. You redact a portion of the column data. For example, you can redact most of a Social Security number with asterisks (*), except for the last 4 digits.
- Regular expressions. You can use regular expressions in both full and partial redaction. This enables you to redact data based on a search pattern for the data. For example, you can use regular expressions to redact specific phone numbers or email addresses in your data.
- Random redaction. The redacted data presented to the querying user appears as randomly generated values each time it is displayed, depending on the data type of the column.
- No redaction. This option enables you to test the internal operation of your redaction policies, with no effect on the results of queries against tables with policies defined on them. You can use this option to test the redaction policy definitions before applying them to a production environment.
Oracle Key Vault
Oracle Key Vault enables customers to easily deploy encryption and other security solutions by offering robust, central management of encryption keys, Oracle Wallets, Java KeyStores, and credential files.
Oracle Key Vault enables customers to quickly deploy encryption and other security solutions by centrally managing encryption keys, Oracle Wallets, Java KeyStores, and credential files. It is optimized for managing Oracle Advanced Security Transparent Data Encryption (TDE) master keys. The full-stack, security-hardened software appliance uses Oracle Linux and Oracle Database technology for security, availability, and scalability.
Oracle Database Vault
Oracle Database Vault implements powerful security controls within Oracle Database. These unique security controls restrict access to application data by privileged database users, reducing the risk of insider and outside threats and addressing common compliance requirements.
Oracle Database Vault security controls help organizations address compliance with data privacy laws and standards such as the EU General Data Protection Regulation (GDPR), the Payment Card Industry Data Security Standard, and numerous other regulations that require strong internal controls on access, disclosure, or modifications to sensitive information.
Oracle Audit Vault and Database Firewall
Oracle Audit Vault and Database Firewall (AVDF) provides a sophisticated next-generation SQL grammar analysis engine that inspects SQL statements going to the database and determines with high accuracy whether to allow, log, alert, substitute, or block the SQL. Oracle AVDF supports white list, black list, and exception list based polices. A white list is simply the set of approved SQL statements that the database firewall expects to see. These can be learned over time or developed in a test environment. A black list includes SQL statements from specific users, IP addresses, or specific types that are not permitted for the database. Exception list-based policies provide additional deployment flexibility to override the white list or black list policies. Policies can be enforced based upon attributes, including SQL category, time of day, application, user, and IP address. This flexibility, combined with highly accurate SQL grammar analysis, enables organizations to minimize false alerts, and only collect data that is important. Database Firewall events are logged to the Audit Vault Server enabling reports to span information observed on the network alongside audit data.
Oracle Data masking and Subsetting
Oracle Data Masking and Subsetting helps improve security, accelerate compliance, and reduce IT costs by sanitizing copies of production data for testing, development, and other activities and by easily discarding unnecessary data.
Oracle Label Security
Oracle Label Security uses row level data classifications to enforce access controls restricting users to only the data they can access. It enables organizations to control their operational and storage costs by enabling data with various levels of sensitivity to co-mingle within the same database. Oracle Label Security also provides a cost-efficient way to address regulatory requirements for managing access to data on a need to know basis.
