Oracle Identity Cloud Service (IDCS) protects Oracle IaaS, PaaS, SaaS and On-Premises applications. Oracle IDCS provides federated single-sign on experience to its clients. It follows open standards such as SAML 2.0, OAuth 2.0 and OpenID Connect 1.0. In the federation model, Oracle IDCS can either act as an Identity Provider (IdP) or a Service Provider (SP) or both.
Oracle IDCS has a built-in feature that provides multiple social identity providers such as Google, Facebook, LinkedIn and Twitter. It uses underlying OAuth 2.0 protocol to interact with the Social Identity providers. This article presents how to configure IDCS to allow for Social Logins. Let me explain this concept with the sequence diagram below:
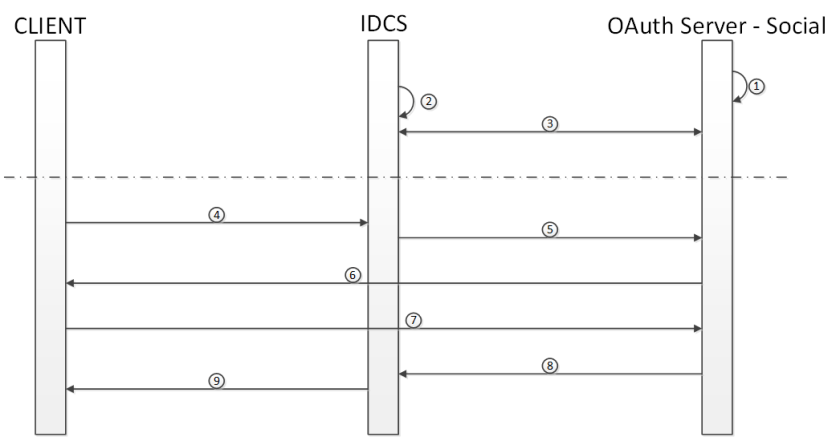
- In OAuth2.0 Server we create an application that is going to be a client to the OAuth Social Server (LinkedIn in this case). This step creates the Client ID and Secret
- Creation of LinkedIn as Social Identity Provider in IDCS. We supply the client id and secret from step 1 as a part of the process
- Establishment of trust between Oracle IDCS and OAuth Server
- Client or user goes through the Social Identity Provider in order to sign into Oracle IDCS
- LinkedIn presents a challenge dialog box in order for client to provide credentials
- LinkedIn server verifies the client credentials and provides the Access Token to IDCS
- Browser redirects to the IDCS website
When there is no social login configured in IDCS we have the following login experience as depicted in the screenshot below:

The following presents steps to configure social login (for example LinkedIn) in Oracle Identity Cloud Service:
Step 1: Configure Social Login IdP using LinkedIn Account
- Go to LinkedIn Developer site
- https://developer.linkedin.com
- Login with your linkedin account. Create one if you do not have it
- “Click My Apps”
- Click “Create Application” – fill-in the details and submit

6. After submitting we see the following information:
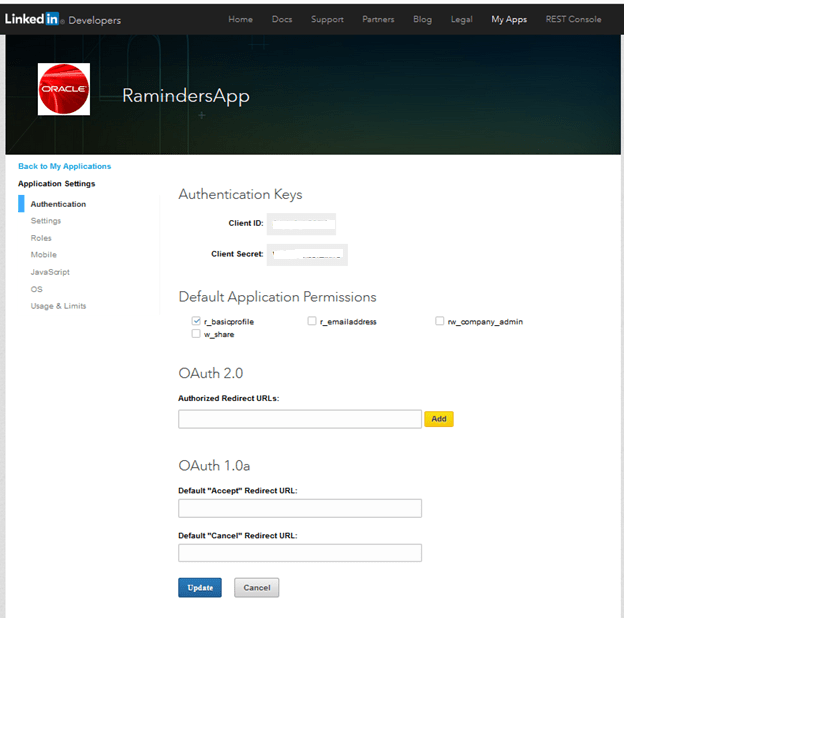
7. Copy the Client ID and Client Secret and input the following URL into OAuth 2.0 Authorised Redirect URLs : https://<Your Oracle Cloud URI>/oauth2/v1/social/callback and click “Update”
Step 2: Configure Social IdP in Oracle IDCS
- Go to Oracle IDCS Admin console i.e. <Your Oracle Cloud URI>/ui/v1/adminconsole
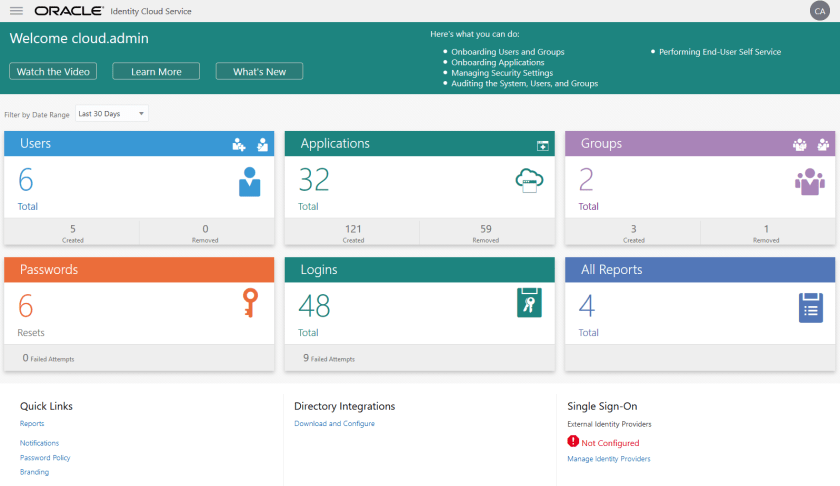

2. From the Home Page go to “Manage Identity Providers” link and chose “Add Social IDP” option as depicted in the screenshot below:

3. From the dropdown menu choose LinkedIn as a type of Social IDP and fillin the Name and Description and press next:
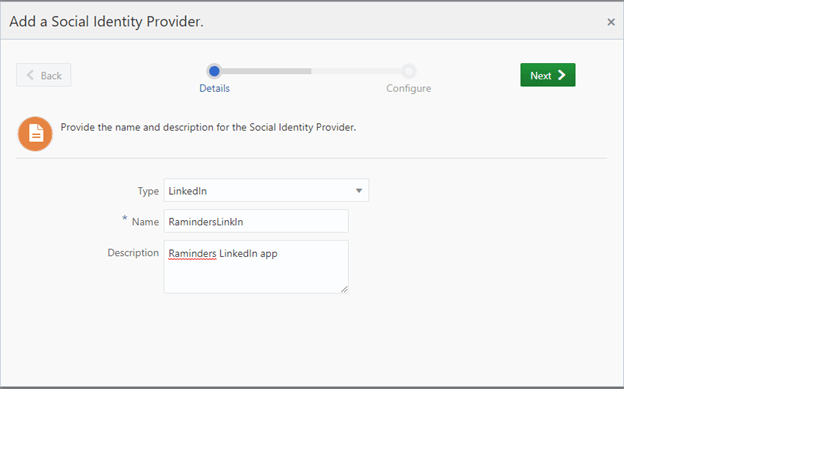
4. Fill-in the Client ID and Client Secret fields from the LinkedIn App saved entries and press Finish:

5. Now Activate the Social IdP and Press “Show on Login Page” as depicted in the screenshot below:

6. Register the Social IdP in the Default Identity Providers list
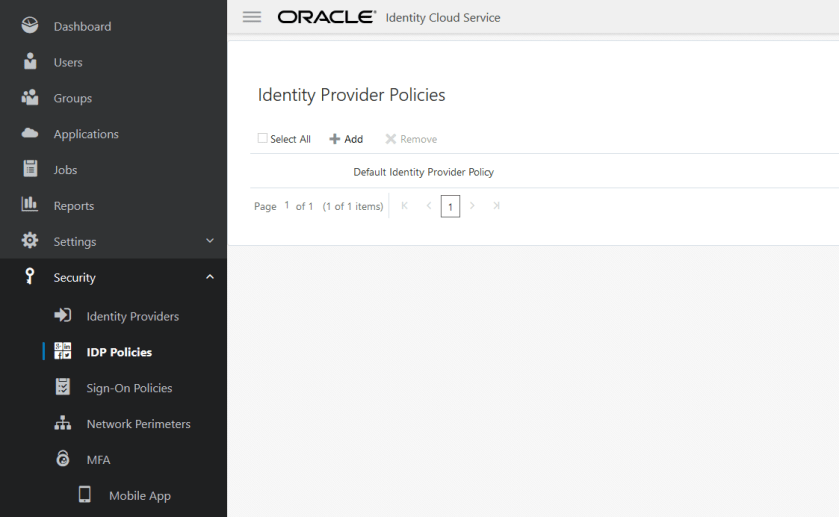
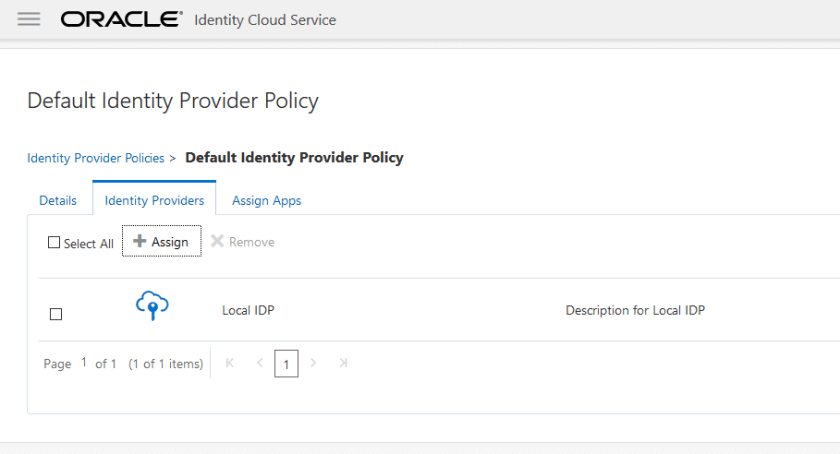
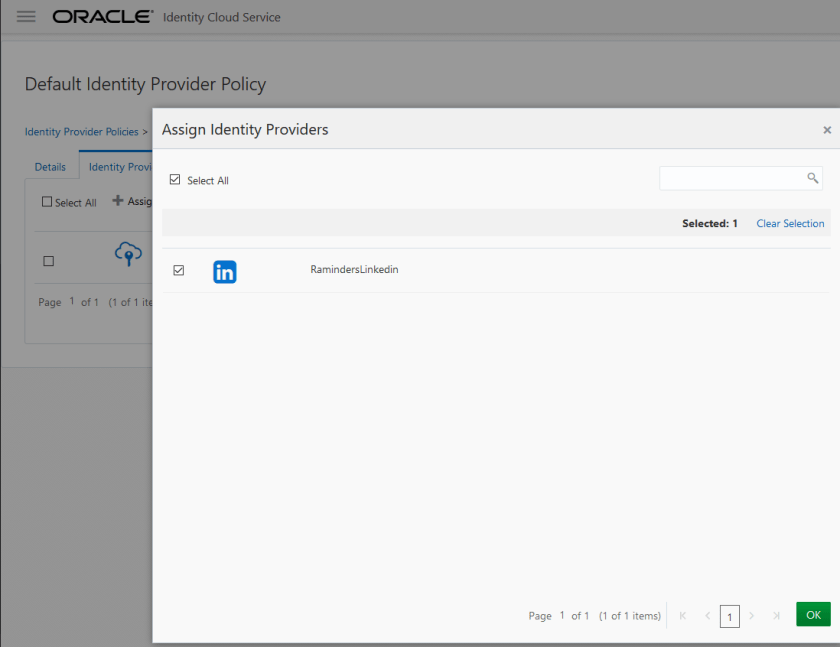
7. Now Logout from the session and we will be presented with the following option for a social login
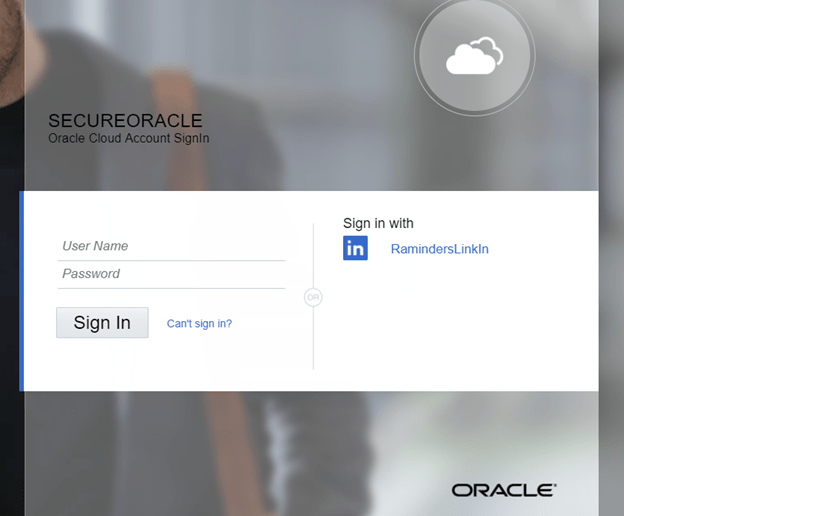
Step 3: Logging into IDCS “myconsole” via LinkedIn
Now we can login via LinkedIn session as depicted in the screenshot below:
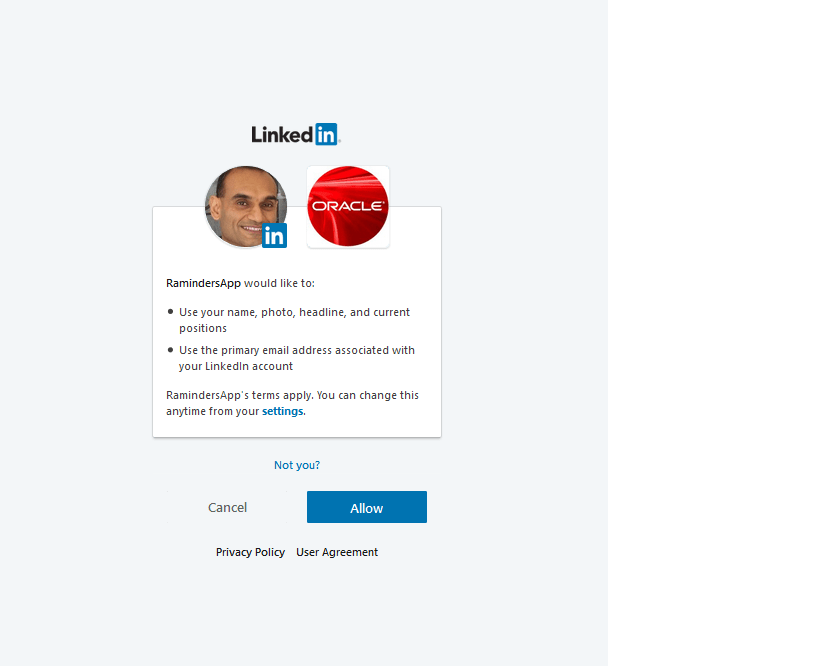
On Entering the UserId and Password for the LinkedIn we see the MyConsole for our LinkedIn user (who unfortunately doesn’t have any access by default, but that is a problem for another time).