I am using the pre-built virtual image that Oracle provides as a public VM in OTN (http://www.oracle.com/technetwork/middleware/soasuite/learnmore/soa-vm-2870913.html). If you don’t have an existing environment, you can download this VM and use it as part of the following exercises.
In this section we are going to review the steps to configure an LDAP adapter. The very first thing that we need to do is to install an LDAP server.
Installing an LDAP server
In this example we are going to use ApacheDS as both LDAP server and Apache Directory Studio as LDAP browser.
- Download and install Apache Directory Studio from http://directory.apache.org/studio/ – Once you download it, simply un-package it where you want to run it from. If you are using the pre-built VM. It should be already within /home/oracle/ldap folder.
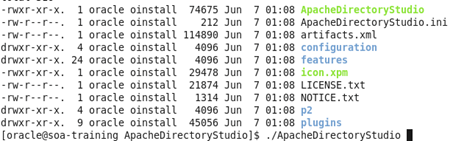
- Start it up, by going within the ApacheDirectoryStudio folder and running ./ApacheDirectoryStudio
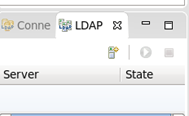
- Next create an LDAP server. Click the LDAP server tab in the bottom left corner and click New Server.
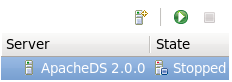
- Select ApacheDS 2.0.0 and click finish.

- Now you can start the server by selecting it and clicking the green play button.
Create a connection to the LDAP server
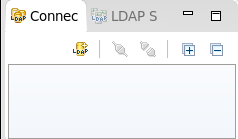
- Next to the LDAP Servers tab, there is a Connections tab. Create a new connection.
- Give whatever name you want, but use localhost and port 10389.
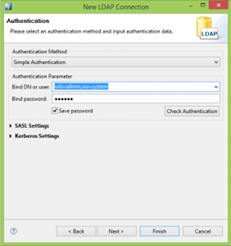
- Click Next and fill in the following credentials: Bind DN or User: uid=admin,ou=system and Bind password: secret
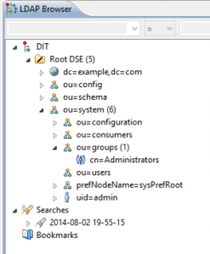
- Click Next until Finish. Now you can now connect to your newly created server and browse it.
Configuring WebLogic
-
Similarly as we did for JMS and DB adapters, in WebLogic Server you need to configure a connection factory in the adapter configuration. First login to WebLogic console and click on the LdapAdapter.
NOTE: The adapter is by default not targeted, although if you are using the pre-built VM it is already targeted to the AdminServer and Active. Ensure that this is the case.

-
The LDAP connection factory is required in order to access by the adapter via JNDI (same as with any other of the JCA technology adapters).
-
Go to the configuration of the LdapAdapter, Outbound Connection Pools and create a New Connection Factory.
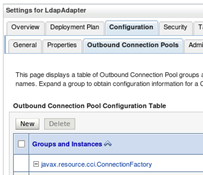
- Give the name eis/ldap/master
-
Once created click on it and provide the following settings, then click Save.
- bindDN: uid=admin,ou=system
- hostname: localhost
- port: 10389
- password: secret

- Similarly as in the previous JCA configurations, rename the deployment plan to something like ldapPlan.xml
-
After the configuration is complete, restart the server. You can do this by going to the desktop of your pre-built VM and use the “WebLogic Control” utility.
The LDAP Adapter cannot be updated like the DB Adapter. This is because the adapter is deployed upon server start, upon which the configuration change is applied.
Configuring the LDAP Adapter
- Create a new SOA project, within your current Application. Call it whatever you want, for example: TestingLDAPProject
- In the composite editor, drag the new LDAP adapter to the References lane (right) to start configuring.
- Call it whatever you want and click Next
-
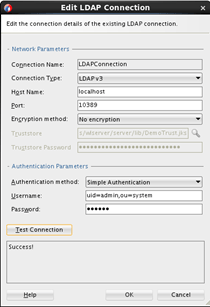
Then create a new Connection by clicking on the green plus icon. Apply the following configurations:
- Hostname: localhost
- Port: 10389
- Encryption method: No encryption
- Authentication method: Simple Authentication
- Username: uid=admin,ou=system
- Password: secret
- Then Test the connection and make sure that it works. Then click OK
- Coming back to the Service Connection window, enter the JNDI name that you specified in the LDAP Connection factory, this case eis/ldap/master

Then click Next.
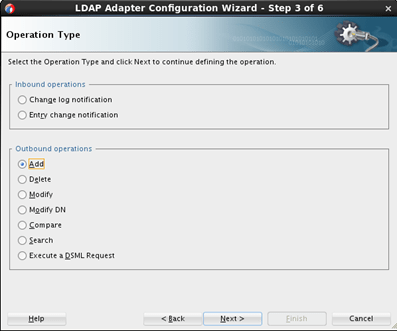
- Choose ‘Add’ as the outbound operation. Then click Next
- Use the following object classes: inetOrgPerson and person. Then use uid and userPassword as fields respectively. That is select inetOrgperson and then it will show the available fields for that class. This should look like this:

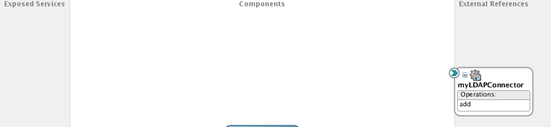
- Click Next until Finish. Your composite should look like this:
Consuming the LDAP Adapter
- Similarly as we have created the BPEL services, create a new Synchronous BPEL with its own exposed service. Use the default 1-string field for input and output. Then wire it to the LDAP adapter.

- Use the following settings:
- In the BPEL return a simple “OK” message if successful.
- Then when implementing the BPEL Invoke action, assign the inputVariable as the uid. Set the password to default “secret” (they should be at least 5 characters and should not contain the username).
- Set the dn element to be of the form: uid=[inputvariable],ou=users,ou=system – For this use a simple concat XPATH function in the Expression Builder
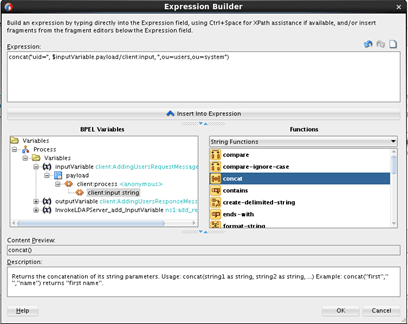
-
Set cn, sn and uid to point to whatever string we send as part of the inputVariable – Your assignment should look like this:
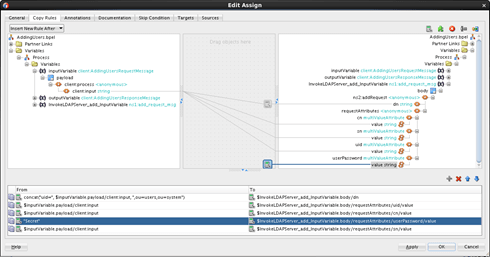
Important: Make sure to wire the actual value elements. If you wire it incorrectly or if you set a String to the parent elements and not the value, it will fail at runtime. For example, in the picture above, notice that I am setting each of the “value” elements and not the actual parents.
- Don’t forget to also set your outputVariable to “OK”. Then Save All.
Testing your LDAP Adapter
- Build and deploy your composite. Ensure you don’t get any errors.
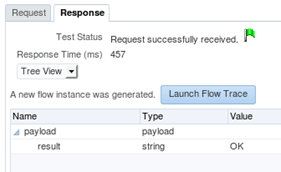
-
Then go to EM Fusion Middleware Control console and send a Test. If everything works, you should be creating a user with specified name in the input text field. Make sure you don’t get errors and that the BPEL replies back with an “OK” message.
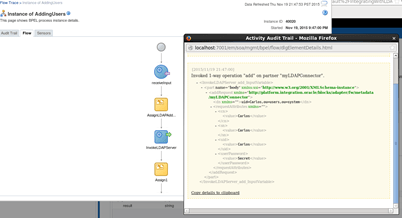
- Analyse the Flow trace and then drill down into the invoke of the BPEL service
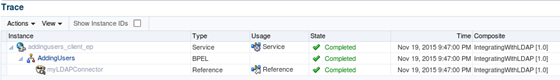
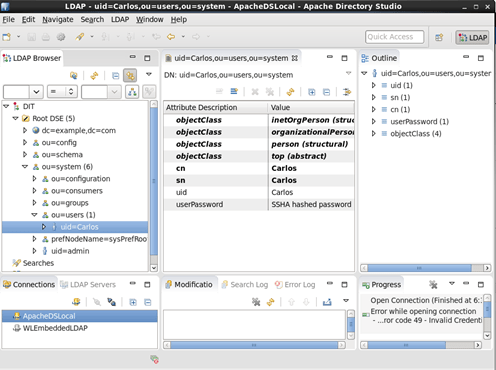
- Go to Apache Directory Studio and reload the entries. You should see the user that you just created.
Congratulations, you have successfully integrated to an LDAP via the Oracle LDAP Adapter. Other use cases for the adapter could be if you have users stored in different systems and want to create users in all of them by means of a single service call or if you want to use information (such as groups or e-mail addresses) available from a provided LDAP server. Using the LdapAdapter, you can provide an abstraction to certain LDAP operations by means of services and make the LDAP server part of the integration effort instead of leaving it out or having to build manual integrations for it.


HI, thanks for great share, I would like to know how to use “Modify outbound operation”.
LikeLike